Key Management: Securely Locked Away
At correctional facilities, the environment is highly structured to ensure that security, safety and order can be maintained. Security procedures are clearly defined and include am...

At correctional facilities, the environment is highly structured to ensure that security, safety and order can be maintained. Security procedures are clearly defined and include among others, head counts, inmate movement tracking, visitor logs and cell inspections. Among the most closely guarded and stringent policies and procedures is key control.
To meet these requirements, facilities across the country are turning to automated key control and management systems. The systems deliver an updated approach to key management security that offers significant improvements over manual systems as well as providing a higher level management tool rather than just a way to control keys. In fact, many states have implemented policies stating that each facility shall have a system for key control that includes firstly the absolute control of keys by staff, secondly the production of key issuance records and thirdly a system which ensures that missing keys are immediately identified. This functionality helps key control and management systems meet the guidelines for correctional institutions.
Layered Access
An automated key control system can minimize the potential for keys to be compromised by restricting access and making them available only to authorized users. High security keys, including Folger Adam keys as well as non-security keys, are securely fastened to a key fob that contains a memory chip. This feature ensures that each time a key is taken from or returned to the key cabinet, the activity is recorded. Users have access to keys only as approved by the system administrator and must enter a PIN or biometric information to access a key. The other keys will remain locked into place when the user accesses the key cabinet to remove or return a key.
Key rings can also be conveniently stored in the key control cabinet with storage of multiple keys on a single key ring where necessary. Tamper-proof locking mechanisms and unique identification systems offer the flexibility to add or remove keys without destroying the ring.
Typically built from stainless steel, key control cabinets are designed to resist abuse and are wired to alarm against tampering. An alarm will also sound if either an invalid user code is entered multiple times consecutively, the door is left open for more than a set number of seconds after use or when a key is missing or not returned on time or returned by the wrong user. Each key storage system is powered by AC electricity and supported by a backup power supply.
Written Evidence
Automated key control systems offer several advantages over manual systems; one of the most powerful is the system's reporting capability. Key control data management software can run the activity reports, sort search results based on different criteria and view and print reports. Corrections personnel can generate practical management reports which trace key movements by time, date and user code as well as audit reports that track keys in use and overdue keys, inconsistent key usage and database listings that show how the system is programmed.
When data is incorporated into correctional facility policies and procedures, it is possible to provide timely information to management for intelligent response, such as rule-based, predefined actions determined by events.
Key Accountability
Automated key control systems can help reduce procedural/policy improprieties as management will always know who removed any key and when it was taken. Guards and other authorized users have access to keys only as approved by the system administrator. For example, day shift personnel can be prohibited from accessing keys outside of their regularly scheduled working hours or accessing keys to which they are not authorized such as the pharmacy or medical areas. Personnel might also be forbidden from exchanging keys during or at the end of a shift because the system will notate that a key was not returned or that it was returned by another user.
Compared to manual key control systems, computerized key control systems offer significant accountability advantages. Individual keys stored in computerized key control systems need not be labeled as to their purpose. If a key is lost, not only does the system flag the missing key, but it also eliminates any immediate identity issues. And when the system is network connected, the advantages are multiplied. For instance, priority email alerts can be sent to supervisors to inform them of the whereabouts of specific keys or a user who has taken a specific key can be denied egress from the facility until the key is returned. Automated key control technology can help administration meet restrictive safety guidelines and help to make a correctional facility a safer place as well.
Business Partner
Morse Watchmans2 Morse Road
CT 06478 Oxford
UK
most read

Is Your Venue Ready for Martyn’s Law?
Martyn’s Law demands stronger security by 2027. Is your venue prepared to protect and respond?
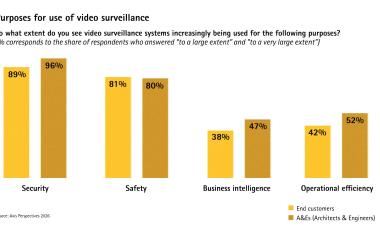
Axis Perspectives Report 2026: How Intelligent Video Technology Strengthens Security and Transforms Business Processes
Axis Perspectives report shows how intelligent video technologies strengthen security and optimize business processes

CRA in Mechanical Engineering: How Companies Manage Risks, Select Secure Components and Protect OT Networks Despite the Lack of Guidelines
How machine builders manage risks and select safe components in accordance with IEC 62443 despite unclear CRA specifications

Salto Systems: From a Bold Idea to a Global Access Ecosystem
25 Years One Jump Ahead

Airbus Defence and Space: Security as a strategic pillar of Europe's defense capability
Airbus Defence and Space protects sites, technologies and employees with modern security and cyber solutions - strengthening Europe's resilience in uncertain times