
Home Security and Automation in One Combined Unit
Although utilizing similar protocols and methods of connection, the worlds of home security and home automation have tended to develop as two separate systems until now. Ksenia has...

Although utilizing similar protocols and methods of connection, the worlds of home security and home automation have tended to develop as two separate systems until now. Ksenia has...

It was 40 years ago, in a coffee house in Kyoto, that the idea of Optex was born. Toru Kobayashi, an electronics engineer, and three like-minded colleagues shared a vision for a ne...

Hikvision and Milestone Systems are supporting a project to find an innovative solution for improving safety and security along the waterfront in Aalborg, Denmark. They teamed up w...

In this expert interview, Dr Eva Maria Buchkremer describes how Innosent resolves a customer challenge and sets new standards with advanced technology. In recent years, Innose...

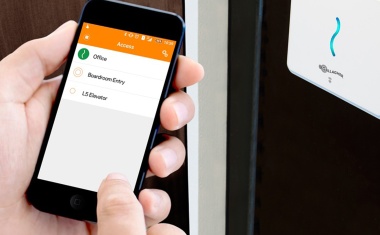
As the Wireless Access Control Report 2018 recently highlighted, more and more organizations are switching to wireless access control to secure their premises. Wireless devices off...

At MIPS 2019 in Copenhagen Milestone Systems has presented their new global digital platform, Milestone Marketplace, with the aim to increase the availability of community-created ...

Access control systems and their components have historically been designed and manufactured in a proprietary way. This approach has made achieving interoperability between differe...

Companies like to trust video surveillance systems to keep watch on their premises and their parking lots. They can react quicker if danger threatens and can already deter potentia...

Following the disastrous fire at Grenfell, it was reported that the intumescent cavity closers, installed as part of the external elevation, were the wrong way around. This meant t...

There is a famous saying, Keep your Secrets Under Lock and Key. Morse Watchmans is proud of their history and their story of how they have successfully helped businesses around the...

Hikvision released the first version of its Product Security White Paper, introducing the security challenges of IoT products and sharing Hikvisions practices to continuously impro...

It was 40 years ago, in a coffee house in Kyoto, that the idea of Optex was born. Toru Kobayashi, an electronics engineer, and three like-minded colleagues shared a vision for a ne...

With security an ever more pervasive concern, the challenges for professionals, on which the exhibition will focus, are continuing to grow. And in the run up to the event, the inte...

The windy city is home to the Sears tower, the Hancock and, infamously, was also home to mobsters like Al Capone during the prohibition era. Chicago has reportedly a population of ...
The security industry and encryption standards must evolve quicker than the use of advancing technology by organised crime, terrorists and chancers to make sure we are all protecte...

VSaaS, or Video Surveillance as a Service, refers to hosted cloud-based video surveillance. The service typically includes video recording, storage, remote viewing, management ale...

The roots of Grundig Intermedia and thereby also of Grundig Security lie in the traditional German Grundig company. Founded in 1945, it became known worldwide for its radios and ...

Decades of experience, innovative ideas, a strong commitment to quality, and a full range of first-class offset printing services: Mohn Media Mohndruck GmbH, a company of the Berte...

The Security Event, its first edition, was launched at the NEC in Birmingham running for 3 days from 9 to 11 April. Alongside its already established cousins, The Fire Event, The H...

Taking place at 18-20 June at Excel London, the event brings over 27,000 visitors together with over than 500 exhibitors, showcasing more than 10,000 security products alongside a ...

When it comes to access control, Salto Systems is always looking to push boundaries and expand the scope of what is possible. For two decades, the Spanish company has been developi...

e-shelter security was formed in 2003, in order to guarantee the physical security of e-shelter data centres. Since then, e-shelter security has developed into a leading technology...

Maintaining an educational environment that is conducive to learning requires, at a minimum, that we keep our school children safe and secure. Its easier said than done, given the ...

In light of more and more organizations switching to wireless access control systems, Assa Abloy presents their wireless access control solutions for higher flexibility and added s...
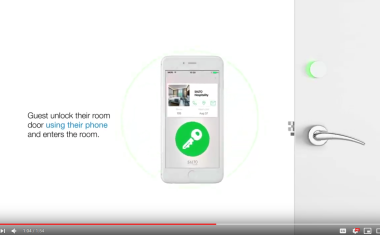
Energy usage is one of the highest operating expenses the hotel industry incurs and remains the second-largest cost hotels have to contend with, right behind labour. The cost of el...
Executives from Johnson Controls, Microsoft and the Middle Easts sustainability pioneer, Beeah, recently announced an agreement to enhance Beeahs new headquarters with a sweeping a...

A massive investment in several big cat and large carnivore enclosures has come to fruition at one of the UKs most popular safari parks. Surroundings Longleat Safari Park in Wil...

When Foxlake Dundee, a new water adventure centre opened in the heart of the Scottish city, Webster Security Fire approached the facilitys management with a novel after-hours surv...

Industrial fire detection specialists Patol have demonstrated the particular suitability of their transit heat sensor to coal conveying applications with a new video shot at Wales ...

Safety and security should never be taken lightly. It only takes one weak link in a security network to turn a potential threat into a serious event that could put lives, data, and...

Aston University, Birmingham, is transforming security and safety with the introduction of SafeZone for students and staff on campus and those travelling globally. The SafeZone so...
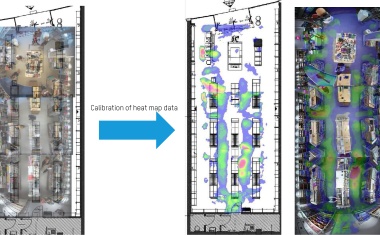
The retail industry is constantly looking to find new ways to be relevant in the ever-increasing shadow of online shopping. Researchers have predicted a 17.5 percent growth in the ...

An access control system is a significant long-term investment but one that, chosen well, can give a host of valuable benefits. We recommend taking it step-by-step to select an acc...

Get to know inspirational characters of the Security Industry in GIT SECURITYs series. Name: Christina Duffey, CPP Position, Company: 2019 ASIS International President, SVP/...

Originally formed as purely an online shop, Bikepirat.at has grown rapidly in just a few years to become Austrias largest specialist bicycle retailer. The company relocated to its ...