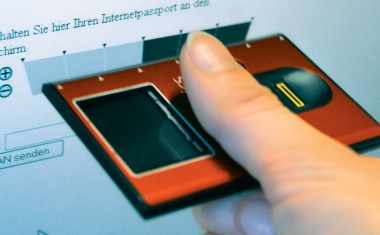
Dallmeier presents combined module for data protection and data security
The EU General Data Protection Regulation (EU GDPR) affirms the great importance of data protection and data security, but does not spell out any regulations relating specifically ...